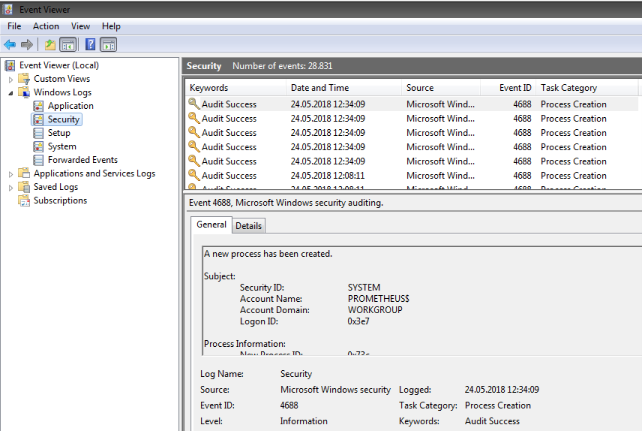
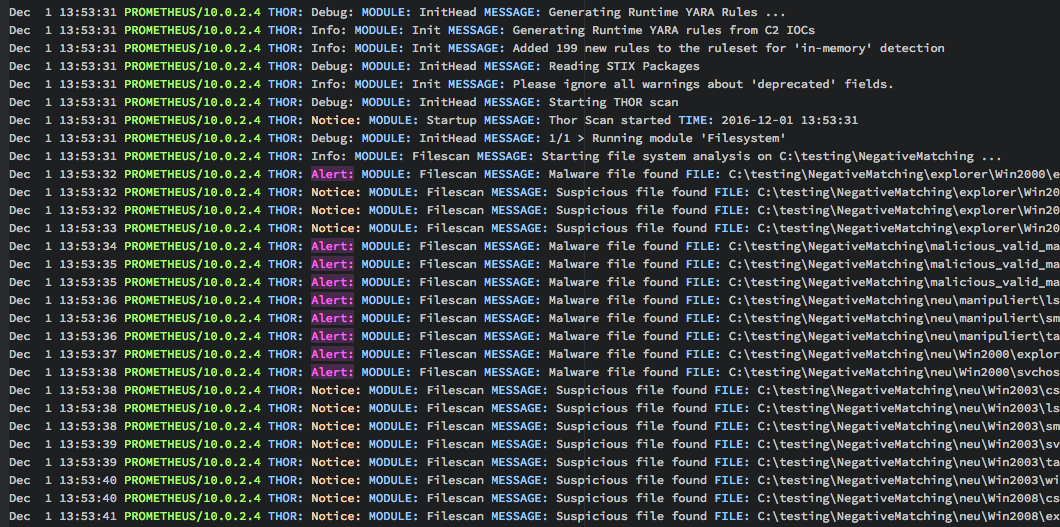
Nextron Systems on X: "THOR APT Scanner Registry Detection Examples - malware, manipulations, cache entries, backdoors, anomalies #DFIR #APT http://t.co/31lIk2GFH2" / X

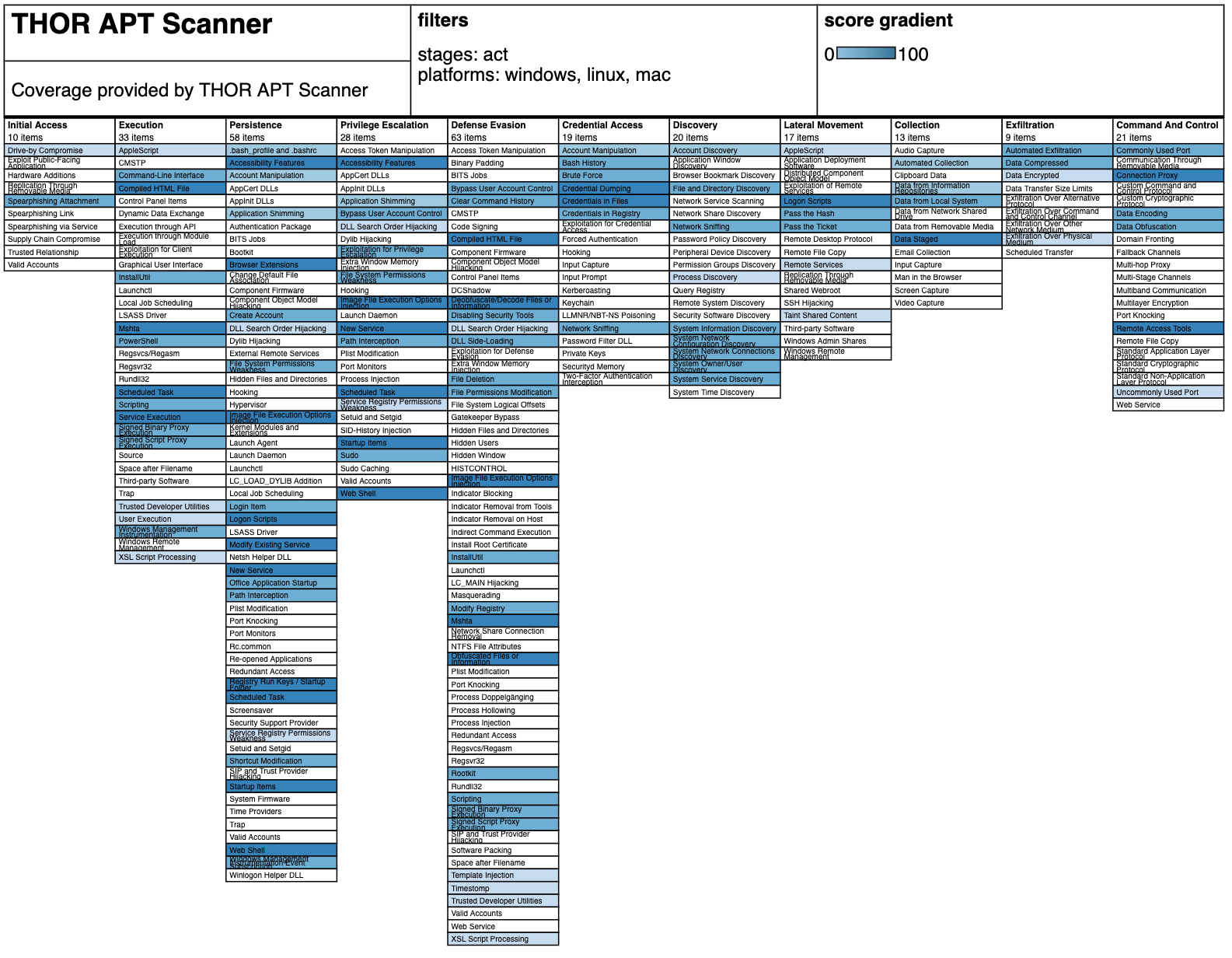
THOR APT Scanner on X: "THOR TechPreview 10.7.3 has been released - Email file pareser - Support for more archive formats - Nested archive scanning - HTML report generation refactored - memory
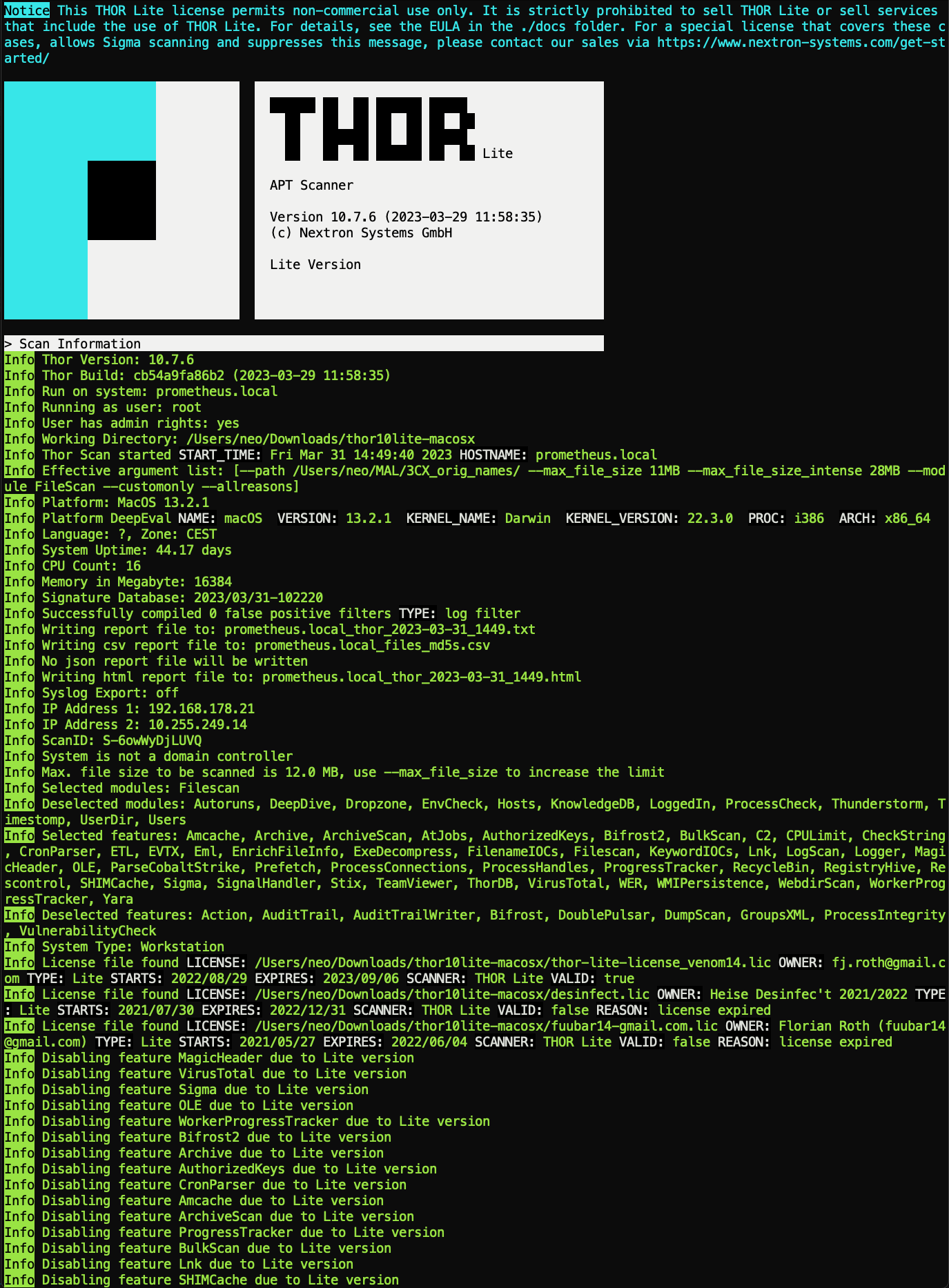
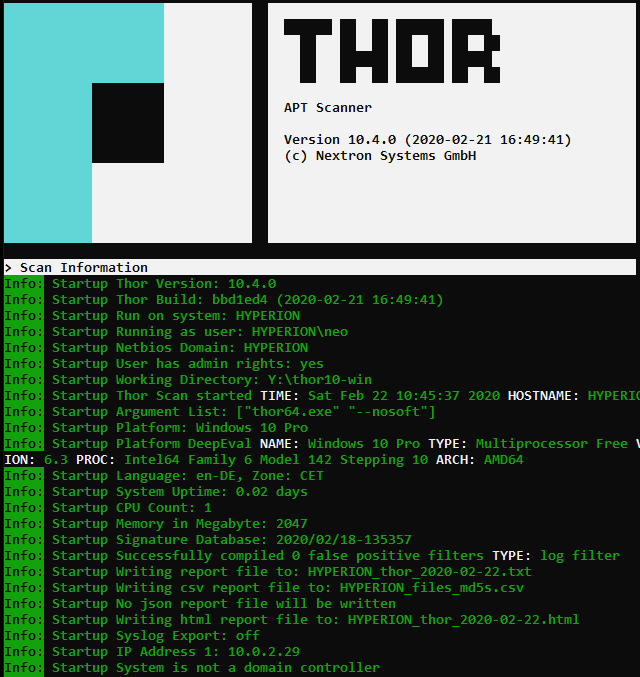
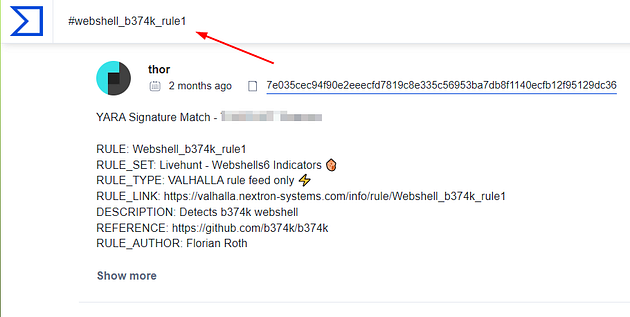
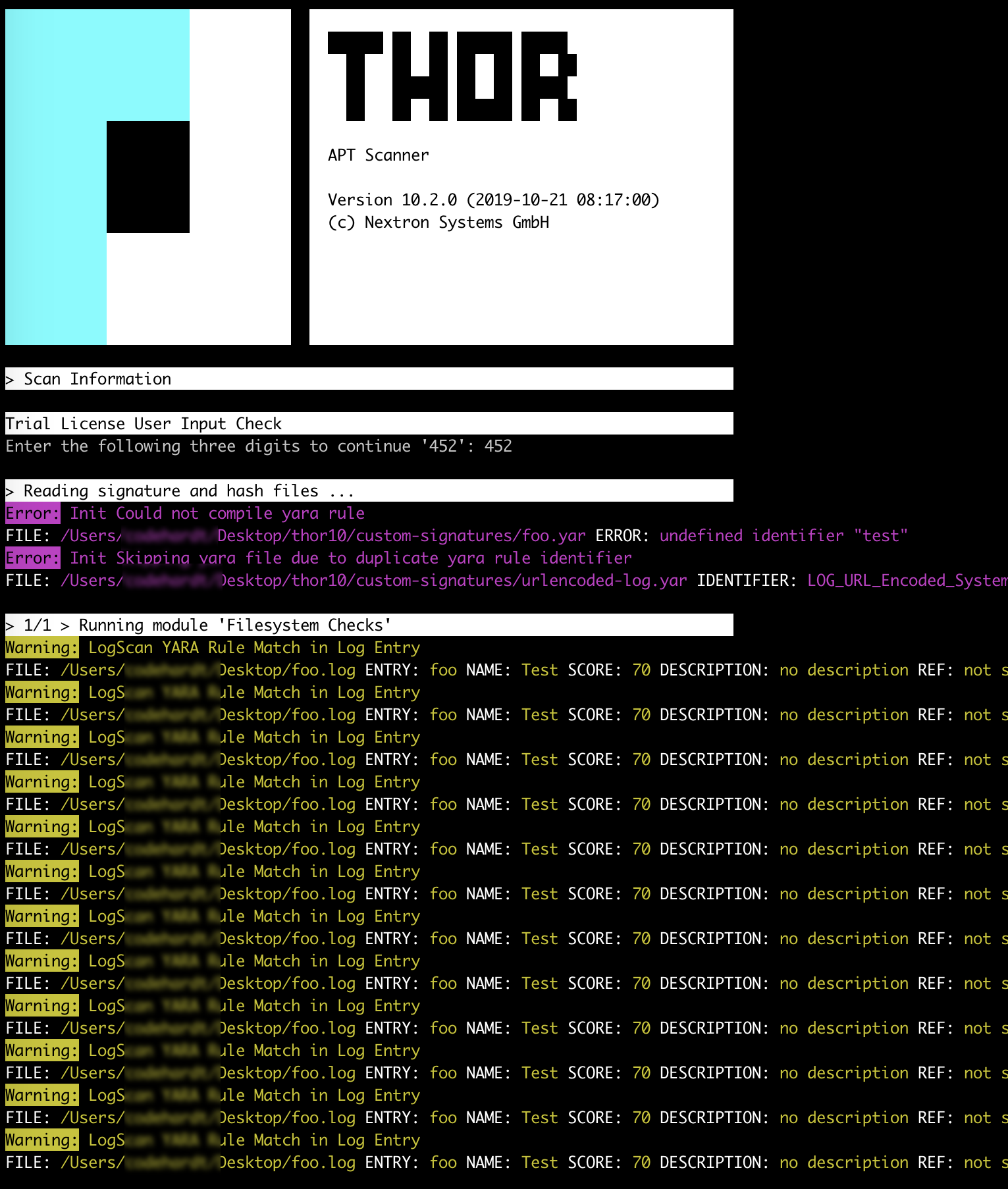
Using THOR Lite to scan for indicators of Lazarus activity related to the 3CX compromise - Nextron Systems